Trezor Login: Securely Access Your Crypto Wallet with Confidence
Everything you need to know about logging into your Trezor wallet safely and managing your digital assets like a pro.
🔐 Introduction: What Is Trezor Login?
When we talk about Trezor login, we’re talking about the gateway to one of the most trusted hardware wallets in the cryptocurrency world. Created by SatoshiLabs, Trezor devices like the Trezor Model One and Trezor Model T are designed to keep your private keys offline — safe from hackers, malware, and phishing attempts. But before you can send, receive, or manage your Bitcoin, Ethereum, or any other crypto assets, you need to understand how to properly log in and connect your Trezor to the web interface or Trezor Suite desktop app.
This article walks you through everything: how to log in, security best practices, troubleshooting tips, and the deeper mechanics behind Trezor’s authentication model. Whether you’re a beginner just unpacking your first device or a seasoned investor optimizing your security workflow, this is your complete guide to Trezor login.
💡 Why Security Matters
Your crypto wallet is not like a traditional bank account. There’s no password reset or “forgot PIN” feature that saves you if your private keys are compromised. That’s why Trezor emphasizes a hardware-first approach — ensuring your keys never leave your device.
🧩 The Role of the PIN & Passphrase
The Trezor PIN and optional passphrase are two critical barriers between hackers and your funds. During login, your device randomly shuffles the keypad layout on-screen, preventing keylogging attacks. The passphrase adds another encrypted layer, effectively creating a hidden wallet.
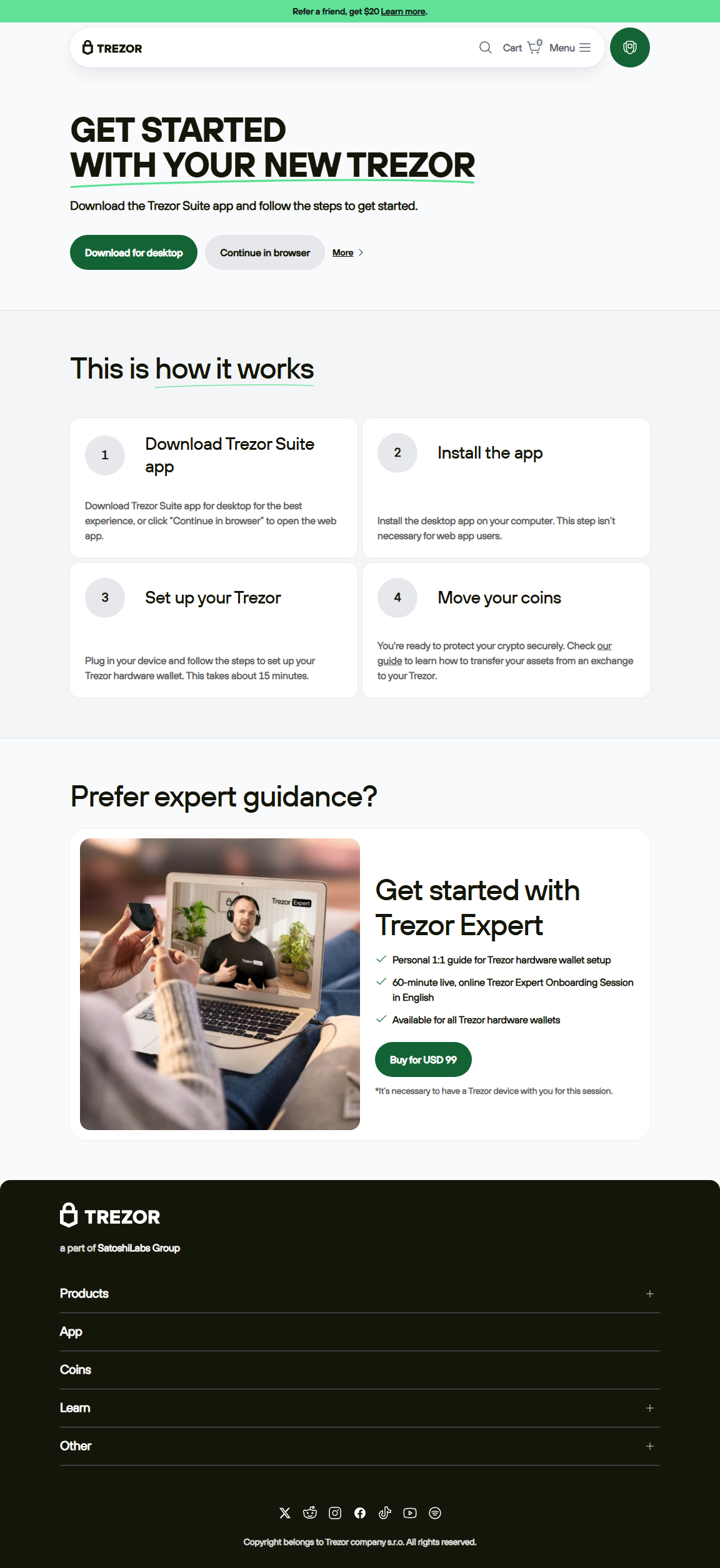
🧭 Step-by-Step: How to Log In to Trezor Wallet
Here’s how to securely access your Trezor account — whether using Trezor Suite desktop, Trezor Web, or a third-party integration like MetaMask or Electrum.
- Connect Your Trezor Device: Plug your Trezor into your computer or mobile device via USB. Ensure your firmware is up-to-date.
- Open Trezor Suite or Go to Trezor.io/start: This interface connects to your device securely. Avoid third-party websites that mimic the official Trezor page.
- Enter Your PIN: A randomized grid appears. Use your device to confirm the correct positions of numbers. This keeps your PIN hidden from your computer.
- Optional: Enter Your Passphrase: If you use a passphrase wallet, you’ll be prompted to enter it. Keep in mind that each unique passphrase opens a unique wallet.
- Access Your Dashboard: Once logged in, you’ll see your portfolio, recent transactions, and the ability to send or receive coins safely.
⚙️ Understanding Trezor Suite: The Core of Trezor Login
Trezor Suite is the official desktop and web interface for managing your crypto portfolio. It provides a user-friendly dashboard to check balances, sign transactions, and monitor portfolio performance in real-time. The interface itself does not hold your private keys — those remain locked inside your Trezor hardware wallet. Instead, it communicates securely through a bridge connection to authorize transactions.
One of the biggest strengths of Trezor Suite is its integration with privacy tools and coin control features. You can choose specific UTXOs when sending Bitcoin, making it easier to manage privacy and reduce traceability on the blockchain. For advanced users, Trezor Suite supports Tor connectivity for anonymous blockchain access — perfect for those who prioritize digital sovereignty.
🧠 Behind the Scenes: How Trezor Login Works Technically
Trezor doesn’t actually "log you in" to an account in the traditional sense. Instead, it uses cryptographic authentication to prove your device ownership and authorize operations. Here’s a simplified look at what happens:
- 1. Device handshake: When you connect your Trezor, the Suite app requests a challenge message.
- 2. Secure signing: Your device signs the challenge using its private key stored in the hardware chip.
- 3. Authentication confirmation: The Suite verifies the signature using the public key, confirming the device is genuine.
This process means your sensitive data never touches the internet — your private key stays offline at all times. It’s a form of zero-knowledge security, making Trezor login one of the safest entry methods in crypto management.
📊 Comparison Table: Trezor vs Other Wallets
| Feature | Trezor | Ledger | Software Wallets |
|---|---|---|---|
| Security | Offline private key storage | Offline storage, secure chip | Online, vulnerable to malware |
| Open Source | ✅ Fully open source | ❌ Closed source firmware | Varies |
| Ease of Use | Simple with Suite interface | Moderate | Easy, but less secure |
| Supported Assets | 1000+ coins & tokens | 1800+ assets | Varies widely |
💬 Common Questions About Trezor Login (FAQ)
Q1: Can I log into Trezor from multiple computers?
Yes. Your Trezor wallet can be accessed from any computer as long as you have your device and PIN. However, never plug it into a public or untrusted machine.
Q2: What happens if I forget my PIN?
You’ll need to reset your device using your recovery seed. This is why it’s essential to keep your 12-, 18-, or 24-word recovery phrase stored offline and never shared digitally.
Q3: Is it safe to use Trezor Web in my browser?
Yes, but always verify the URL (it should begin with https://suite.trezor.io) and ensure your device’s firmware matches the latest version. For maximum safety, Trezor Suite desktop is recommended.
Q4: Does Trezor Login require internet?
While Trezor Suite uses an internet connection to fetch blockchain data, your device itself remains offline. Private keys never leave your Trezor — even when you’re connected.
🔥 Pro Tip: Never Enter Your Recovery Seed on a Website
Scammers often clone Trezor websites and prompt users to “log in” by entering their 12–24-word recovery seed. Never do this. Your seed belongs offline, written down on paper or stored in a metal backup. If a website ever asks for it, it’s a scam.
🚀 Advanced Security Tips for Trezor Login
- Use a unique passphrase for an additional layer of wallet encryption.
- Always double-check addresses on your Trezor screen before confirming transactions.
- Enable the “Remember device” option only on trusted personal computers.
- Update firmware regularly to patch vulnerabilities and enhance compatibility.
- Consider using Tor integration within Trezor Suite for private blockchain access.
🏁 Conclusion: Mastering Trezor Login
The Trezor login process is more than just a way to access your crypto — it’s a statement of ownership and self-sovereignty. With every secure connection, every randomized PIN entry, and every verified transaction, you’re taking control of your digital wealth in the safest way possible. Trezor’s combination of simplicity, transparency, and open-source security continues to make it a cornerstone of the decentralized future.
So the next time you power on your Trezor and connect it to Trezor Suite, remember: you’re not just logging into a wallet — you’re logging into the future of financial freedom.